rage: Rust implementation of age
rage is a simple, modern, and secure file encryption tool, using the age format. It features small explicit keys, no config options, and UNIX-style composability.
The format specification is at age-encryption.org/v1. To discuss the spec or other age related topics, please email the mailing list at [email protected]. age was designed by @Benjojo12 and @FiloSottile.
The reference interoperable Go implementation is available at filippo.io/age.
Usage
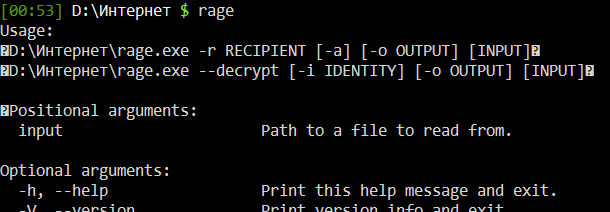
Usage:
rage [--encrypt] -r RECIPIENT [-i IDENTITY] [-a] [-o OUTPUT] [INPUT]
rage --decrypt [-i IDENTITY] [-o OUTPUT] [INPUT]
Positional arguments:
INPUT Path to a file to read from.
Optional arguments:
-h, --help Print this help message and exit.
-V, --version Print version info and exit.
-e, --encrypt Encrypt the input (the default).
-d, --decrypt Decrypt the input.
-p, --passphrase Encrypt with a passphrase instead of recipients.
--max-work-factor WF Maximum work factor to allow for passphrase decryption.
-a, --armor Encrypt to a PEM encoded format.
-r, --recipient RECIPIENT Encrypt to the specified RECIPIENT. May be repeated.
-R, --recipients-file PATH Encrypt to the recipients listed at PATH. May be repeated.
-i, --identity IDENTITY Use the identity file at IDENTITY. May be repeated.
-o, --output OUTPUT Write the result to the file at path OUTPUT.
INPUT defaults to standard input, and OUTPUT defaults to standard output.
RECIPIENT can be:
- An age public key, as generated by rage-keygen ("age1...").
- An SSH public key ("ssh-ed25519 AAAA...", "ssh-rsa AAAA...").
PATH is a path to a file containing age recipients, one per line
(ignoring "#" prefixed comments and empty lines).
IDENTITY is a path to a file with age identities, one per line
(ignoring "#" prefixed comments and empty lines), or to an SSH key file.
Passphrase-encrypted age identity files can be used as identity files.
Multiple identities may be provided, and any unused ones will be ignored.
Multiple recipients
Files can be encrypted to multiple recipients by repeating -r/--recipient. Every recipient will be able to decrypt the file.
$ rage -o example.png.age -r age1uvscypafkkxt6u2gkguxet62cenfmnpc0smzzlyun0lzszfatawq4kvf2u \
-r age1ex4ty8ppg02555at009uwu5vlk5686k3f23e7mac9z093uvzfp8sxr5jum example.png
Recipient files
Multiple recipients can also be listed one per line in one or more files passed with the -R/--recipients-file flag.
$ cat recipients.txt
# Alice
age1ql3z7hjy54pw3hyww5ayyfg7zqgvc7w3j2elw8zmrj2kg5sfn9aqmcac8p
# Bob
age1lggyhqrw2nlhcxprm67z43rta597azn8gknawjehu9d9dl0jq3yqqvfafg
$ rage -R recipients.txt example.jpg > example.jpg.age
Passphrases
Files can be encrypted with a passphrase by using -p/--passphrase. By default rage will automatically generate a secure passphrase.
$ rage -p -o example.png.age example.png
Type passphrase (leave empty to autogenerate a secure one): [hidden]
Using an autogenerated passphrase:
kiwi-general-undo-bubble-dwarf-dizzy-fame-side-sunset-sibling
$ rage -d example.png.age >example.png
Type passphrase: [hidden]
Passphrase-protected identity files
If an identity file passed to -i/--identity is a passphrase-encrypted age file, it will be automatically decrypted.
$ rage -p -o key.age <(rage-keygen)
Public key: age1pymw5hyr39qyuc950tget63aq8vfd52dclj8x7xhm08g6ad86dkserumnz
Type passphrase (leave empty to autogenerate a secure one): [hidden]
Using an autogenerated passphrase:
flash-bean-celery-network-curious-flower-salt-amateur-fence-giant
$ rage -r age1pymw5hyr39qyuc950tget63aq8vfd52dclj8x7xhm08g6ad86dkserumnz secrets.txt > secrets.txt.age
$ rage -d -i key.age secrets.txt.age > secrets.txt
Type passphrase: [hidden]
Passphrase-protected identity files are not necessary for most use cases, where access to the encrypted identity file implies access to the whole system. However, they can be useful if the identity file is stored remotely.
SSH keys
As a convenience feature, rage also supports encrypting to ssh-rsa and ssh-ed25519 SSH public keys, and decrypting with the respective private key file. (ssh-agent is not supported.)
$ rage -R ~/.ssh/id_ed25519.pub example.png > example.png.age
$ rage -d -i ~/.ssh/id_ed25519 example.png.age > example.png
Note that SSH key support employs more complex cryptography, and embeds a public key tag in the encrypted file, making it possible to track files that are encrypted to a specific public key.
Installation
On macOS or Linux, you can use Homebrew:
brew tap str4d.xyz/rage https://str4d.xyz/rage
brew install rage
On Windows, Linux, and macOS, you can use the pre-built binaries.
If your system has Rust 1.51+ installed (either via rustup or a system package), you can build directly from source:
cargo install rage
Note: previously the
ragesuite of tools was provided in theageRust crate. This is no longer the case;agenow only contains the Rust library.
Help from new packagers is very welcome.
Feature flags
-
mountenables therage-mounttool, which can mount age-encrypted TAR or ZIP archives as read-only. It is currently only usable on Unix systems, as it relies onlibfuse. -
ssh(enabled by default) enables support for reusing existing SSH key files for age encryption. -
unstableenables in-development functionality. Anything behind this feature flag has no stability or interoperability guarantees.
License
Licensed under either of
- Apache License, Version 2.0, (LICENSE-APACHE or http://www.apache.org/licenses/LICENSE-2.0)
- MIT license (LICENSE-MIT or http://opensource.org/licenses/MIT)
at your option.
Contribution
Unless you explicitly state otherwise, any contribution intentionally submitted for inclusion in the work by you, as defined in the Apache-2.0 license, shall be dual licensed as above, without any additional terms or conditions.